Stepping Up Your Password Security
August 26, 2021 | By Kevin Smith, CFA
After seeing a friend recently hacked to the tune of $30,000+, I decided to step up my personal data security game. Here is what I learned, and what changes I am making.
All traditional financial accounts like bank accounts and brokerage accounts are held with a custodian such as Chase, Wells Fargo, Schwab, or Fidelity. Their jobs are to make sure that only you can access your account and they conduct transactions for you. They have security protocols in place to protect you from nefarious characters, but if someone has your username and password, they might find a way to get in. That’s where the responsibility falls on the account owner.
How do passwords get stolen? There are too many ways to list (and too technical for me to understand), but the common themes are: a) getting tricked into providing passwords or codes, and b) transmitting password and codes in an unsecured way. The villains are getting better, but so are the security tools. The problem is most of us aren’t using them.
Passwords
Use a lengthy password. A 5-character password is much easier to guess and hack than a 10-character password. I’ve read suggestions from people who seem to be experts that we should use at least 16 characters for common passwords and 25 for critical master passwords.
Use a random password generator. Creating long passwords and making them hard to crack is difficult. Random password generators solve this problem. Any password-saving application will do this, or you can easily find one online.
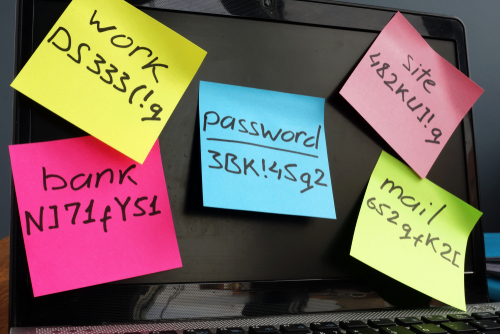
Use a password manager. Now that you have lengthy, randomly-generated passwords, how are you going to remember them? Don’t save them in a Word document! Don’t write them on a notepad next to your computer! Consider using a password manager like LastPass or 1Password. I have used both and they get better all the time. Both platforms use military-grade security and all you have to do is memorize one super-duper long password to unlock all of your random passwords. This saves me at least 15 minutes per day; probably more. It is also a great way to share passwords with family or co-workers.
More than just a password. Turn on multi-factor authorization.
You have almost certainly been required to receive a text message or email code to login to a website. This is called “multi-factor authorization”, and it is a second layer of security. If someone steals your password, they will need to also get that code to log in. Some websites require you to set this up, but it is optional for others. Go to the Settings section of the website, then to Security Settings to see your options. This is something you have to do on your own if you want to maximize your security.
At the very least, set up two-factor authorization with text. This seems to be the most common method, and it is better than nothing, but the text message is not encrypted and it is tied to your phone number, which is vulnerable! I recently learned about the ‘SIM swap’ attack where the evildoer convinces your cell phone carrier to port your SIM to their phone, which means they control your text messages. They could also persuade the phone carrier to forward text messages to their phone. Either way they can easily change your passwords and take control of your accounts. Yikes!
Text message codes are vulnerable to phishing scams. This is where fake websites are created that make it seem very compelling to provide a text message code. None of us think we can be so easily duped, but it happens.
There are a few higher security options that may be available, depending on the website:
- Push codes are sent encrypted over an internet connection to an app on your phone, rather than going through your phone service provider.
- Authenticator apps generate a code using an app on your phone. You don’t need phone service or a Wi-Fi connection for it to work. Most password managers have this available, as well Google, Norton and other anti-virus software providers. A popular version of this is called Authy.
- Push approvals are a way for you to simply push a button that says, ‘yes, that was me’ on an app that pops up on your phone. This is most commonly available when you are logged into an ecosystem like Microsoft or Google. Not having a code reduces the chance of a code being intercepted, but if the perpetrator already hacked your Google account, that would be a problem.
- Security keys may be the highest level of security available for multi-factor authorization. They are small physical devices that plug into your computer’s USB port or can be read by your phone using NFC technology. You can keep it on your key chain. Because it is a physical device confirming your identity with the website, there is no transmission to be intercepted. If you lose it, the thief would still need to have your username and password, and you can easily ‘turn off’ your security key with the website. (I just ordered one called YubiKey.)
Secure internet connections
If you are using public Wi-Fi (like I am while writing this), any data you send and receive can be intercepted, including user names and passwords. It is as secure as a carrier pigeon (possibly less if the pigeon is well-trained and in its prime.)
Consider getting a VPN (Virtual Private Network) service. When you turn on your VPN, your data is sent through an encrypted virtual tunnel. These services are relatively inexpensive and easy to use. I’ve been using NordVPN for several years, but there are many to choose from.
We can have faith in institutions to keep our accounts safe, but there are no guarantees and they can’t prevent us from making our own mistakes. Data security is a personal responsibility.
Return to Blog Page